In today’s evolving security landscape, preparing for the post-quantum era is no longer optional — it’s essential. With the publication of FIPS 203, 204, and 205, organizations now have a clear path to begin deploying post-quantum cryptographic (PQC) standards.
I wanted to take this challenge head-on by building a “production-ready” (deployment-ready) NGINX container image that not only supports classical TLS but also enables hybrid classical + post-quantum key exchanges and signatures.
Here’s how I approached it.
Step 1: The Build Foundation
I started by creating a custom Dockerfile that layers:
- Base Ubuntu image – lightweight but production-ready.
- FIPS-compliant OpenSSL (OQS-OpenSSL3 fork) – adds PQC algorithms.
- NGINX compiled against OQS-OpenSSL3 – ensures TLS handshakes can use PQC.
- Security hardening – stripping, non-root execution, locked-down configs.
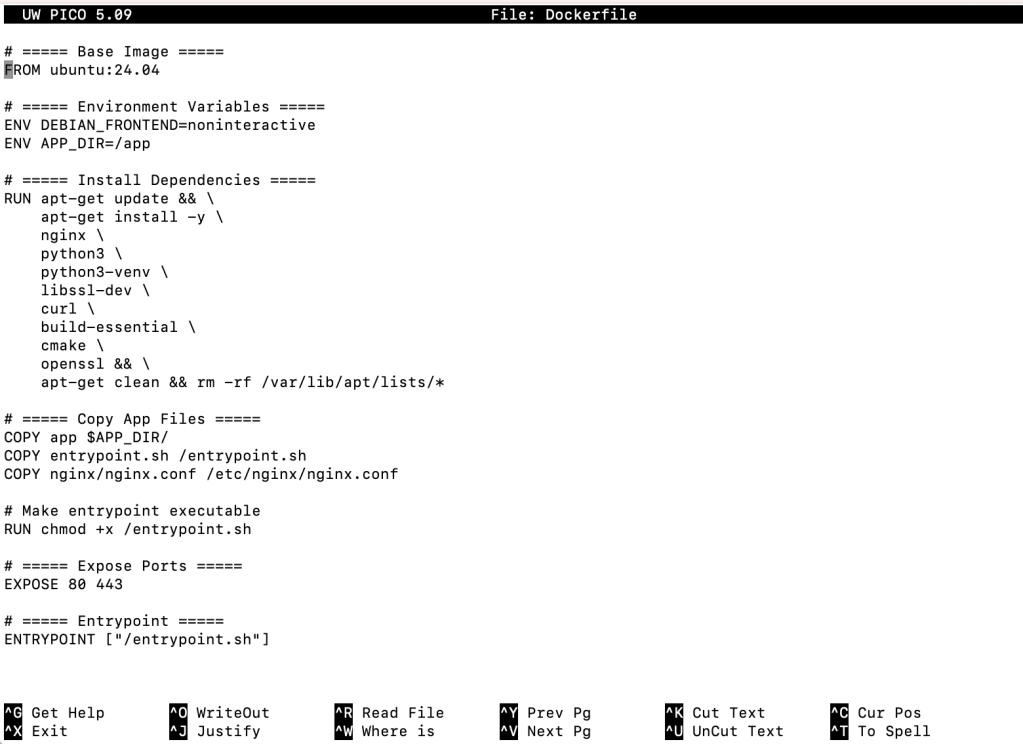
The goal was to produce a self-contained FIPS 203/204/205 ready container, deployable without extra configuration headaches.
Step 2: The Cryptography
The container supports the three NIST-selected PQC algorithms alongside classical algorithms:
| Standard | Algorithm | Role |
|---|---|---|
| FIPS 203 | ML-KEM (Kyber) | Key Encapsulation (TLS handshake, hybrid with X25519) |
| FIPS 204 | ML-DSA (Dilithium) | Digital Signatures (server certs, message signing) |
| FIPS 205 | SLH-DSA (SPHINCS+) | Stateless Hash-Based Signatures (fallback, long-term resilience) |
I set up hybrid TLS flows so the handshake includes both a classical algorithm (RSA/ECDSA/X25519) and a PQC algorithm, ensuring security even if either side is later compromised.
Step 3: Containerized Web Security
The result is a Docker container that:
- Exposes NGINX with PQC-enabled TLS
- Accepts hybrid key exchange: X25519 + ML-KEM (Kyber)
- Supports dual-signatures: RSA/ECDSA + Dilithium/SPHINCS+
- Is FIPS 140-3 forward-prepared by design
Security Flow Table
| Flow | Classical-Only | PQC-Only | Hybrid |
|---|---|---|---|
| TLS Handshake | RSA/ECDSA + X25519 | ML-KEM (Kyber) | X25519 + ML-KEM |
| Signatures | RSA/ECDSA | Dilithium / SPHINCS+ | Dual |
| Compliance | FIPS 140-3 | FIPS 203–205 | Forward-prepared |
Why This Matters
- Future-proofing: Organizations can start testing PQC without abandoning existing TLS stacks.
- Deployment-ready: An experiment — hardened, reproducible, and deployable today “Deployment-ready for experimentation and early adoption.”
- Compliance-first: Aligned with the NIST FIPS roadmap (203/204/205).
This project was about more than compiling NGINX — it was about proving that hybrid post-quantum security can be deployed for testing today. The future of secure web infrastructure lies in containers that make PQC effortless — and this experiment was my first step in that direction.
Leave a comment