In this experiment, I’m capturing and analyzing quantum-safe network traffic using the OQS Wireshark Docker image. The goal is to understand how post-quantum cryptography behaves in real network conditions, verify hybrid TLS connections, and assess whether existing packet inspection tools can still provide meaningful insights without breaking the quantum-safe security properties. Specifically, I’m looking to provide screenshots inside Wireshark to bring the research to life for newcomers, and answer questions such as:
- How do hybrid classical/quantum TLS handshakes appear at the packet level?
- Can standard network monitoring tools detect anomalies or performance impacts introduced by post-quantum algorithms?
- What are the latency and packet size implications of integrating ML-KEM (Kyber), ML-DSA (Dilithium), and SLH-DSA (SPHINCS+) into existing web connections?
- How can we visually or programmatically distinguish classical TLS traffic from hybrid quantum-safe traffic in a pcap capture?
This research aims to provide practical, hands-on insights into deploying and debugging post-quantum cryptography in containerized environments, while documenting it for the broader security research community.
To explore these questions, I’m using the OQS Wireshark Docker image in a controlled lab environment. By running Wireshark in CLI mode inside a container, I can capture packets from hybrid quantum-safe connections without interfering with my host network setup. The process involves starting the container with proper network access, identifying the right interfaces, and saving the packet captures to a location accessible from my host machine. From there, the pcap files can be analyzed to observe the handshake flows, certificate exchanges, and encrypted payload patterns, providing a detailed window into how post-quantum algorithms behave in practice.
To keep things Macbook-friendly I decided to use no-GUI capture + remote GUI, but instead run the container in headless mode to capture packets with tshark (Wireshark CLI), then open the .pcap in my local Wireshark app:
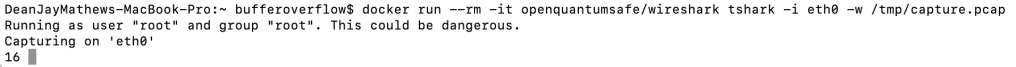
docker run --rm -it openquantumsafe/wireshark tshark -i eth0 -w /tmp/capture.pcap
Then copy the file out of the container (once the container has been stopped) and open it locally using: docker stop <your_container_id>
docker cp <your_container_id>:/tmp/capture.pcap ~/Desktop/capture.pcap
Perfection — the below screenshot means the container is now running Wireshark’s CLI (tshark) and is actively capturing packets on eth0:
Stopping the capture
- Press Ctrl+C in the terminal to stop
tshark. - This finalizes the
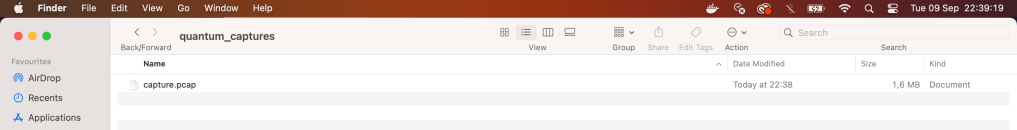
.pcapfile so it can be opened in Wireshark locally. See the .pcap file on my Desktop:
1️⃣ Inspect TLS Handshakes
This will show all TLS handshake packets, including any hybrid classical/quantum extensions:
tshark -r ~/Desktop/capture.pcap -Y "tls.handshake" -V
-r ~/Desktop/capture.pcap→ read your capture file-Y "tls.handshake"→ filter only handshake packets-V→ verbose output (details for each field)
Goal: See how hybrid key exchange extensions (Kyber/Dilithium/SPHINCS+) appear at the packet level.
2️⃣ Measure Latency Between Handshake Messages
You can calculate timing between packets:
tshark -r ~/Desktop/capture.pcap -Y "tls.handshake" -T fields -e frame.number -e frame.time_relative -e tls.handshake.type
frame.time_relative→ relative time since capture start- Compare times of ClientHello → ServerHello → Finished
- Screenshot the timing to show latency impact of PQC algorithms.
3️⃣ Identify Packet Sizes
Check TLS packet sizes to see the impact of hybrid keys:
tshark -r ~/Desktop/capture.pcap -Y "tls.record.version == 0x0303" -T fields -e frame.number -e frame.len -e tls.record.version
frame.len→ length of the packet in bytes- Compare classical vs hybrid packets to highlight size increase from PQC data.
4️⃣ Distinguish Classical vs Hybrid TLS
If you added a custom extension for ML-KEM / ML-DSA / SLH-DSA, filter by its tls.handshake.extension_type (replace with your extension ID):
tshark -r ~/Desktop/capture.pcap -Y "tls.handshake.extension_type == 0x2f2f" -T fields -e frame.number -e tls.handshake.extension_type -e frame.len
Leave a comment