This new micro application is a FIPS 203/204/205 Compliance Certificate Checker that tells you if your security certificate is FIPS compliant or not by checking the status at network endpoints (domains). It not only checks for FIPS compliance, but it also tells you exactly which algorithm is being used currently, and then suggests concrete next steps to achieve your FIPS 203/204/205 hybrid-quantum compliance. You can download and use the app via Docker: fips_cert_checker_app
The logic is tied to FIPS compliance, and explains clearly your current situation and how it differs from a fully FIPS-compliant hybrid classical/quantum TLS certificate. Here are some examples you might see after running your domain through the app:
✅ Classical but FIPS-approved (your cert could become compliant if wrapped with PQ)
❌ Classical and not FIPS-approved (your cert will never be compliant, even with PQ)
✅ Pure PQ (but needs hybrid to be compliant today)
✅ Hybrid (PQ + Classical) (fully compliant if classical side is FIPS-approved)
The app uses a dual-logic approach. First it checks your domain for quantum-safe algorithms as mandated by NIST, then it checks FIPS compliance of the setup in general. It’s a detailed, granular approach so that the system measures with confidence all the requirements mandated in FIPS, such as key length, approved hash functions, et cetera.
Here is the output from running the app against the abconlinecourses.com web domain:
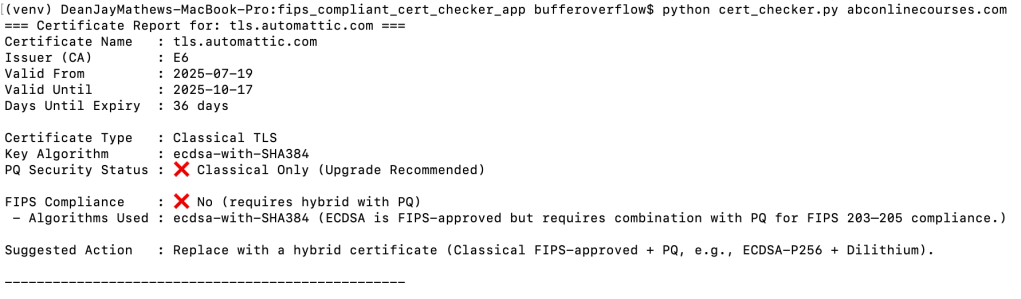
As you can see, the app has explained that the TLW certificate is a classical encryption and therefore not FIPS compliant. Furthermore it has given a full explanation of the situation and also a Suggested Action to become FIPS compliant.
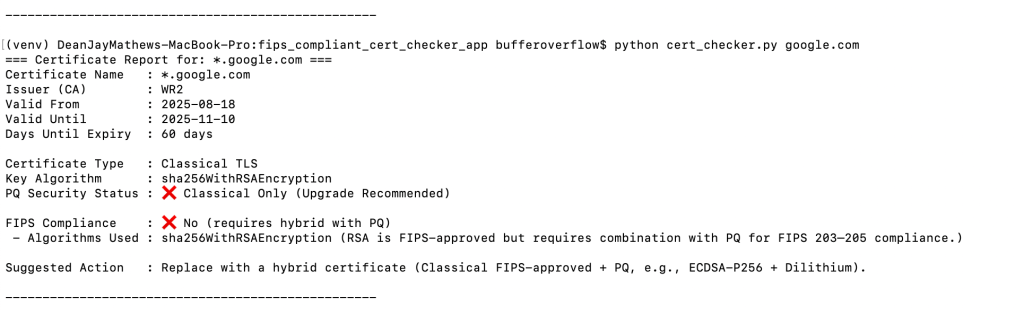
Here are two more examples, running the app against google.com and fbi.org:
GOOGLE.COM:
FBI.ORG:
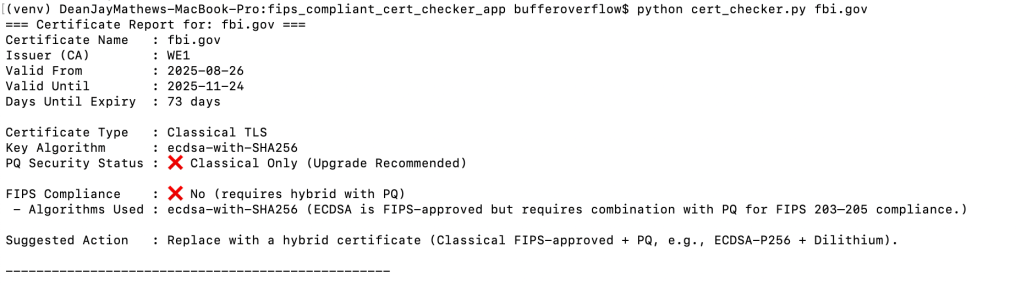
We can see the exact algorithm ABC, Google, and the FBI are using, and what steps they need to take to upgrade to Quantum Safe by 2030.
Let’s look at that dual-logic we mentioned further above:
1. Hybrid / Quantum-Safe Certificate Detection (PQ Status)
Factors to check:
| Factor | How to detect | Why it matters |
|---|---|---|
| Signature algorithm | Look for post-quantum algorithms like Dilithium, Falcon, SPHINCS+ | Determines if the cert resists quantum attacks |
| Key type | If it combines classical key (RSA/ECDSA) with post-quantum key, mark as Hybrid | Hybrid certificates can be deployed today for FIPS-compliant transition |
| Certificate extensions | Some hybrid certs include specific OIDs indicating post-quantum algorithms | Provides explicit indicator for automated detection |
✅ Output logic:
- If classical only →
PQ Security Status: ❌ Classical Only (Upgrade Recommended) - If hybrid →
PQ Security Status: ✅ Hybrid/Quantum Safe
2. FIPS Compliance (203/204/205)
Factors to check:
| Factor | How to detect | Notes |
|---|---|---|
| Approved algorithm | Must be from NIST-approved FIPS list: RSA-3072, RSA-4096, ECDSA-P256, ECDSA-P384 | This ensures the classical part is strong enough |
| Key length | Match approved lengths | E.g., RSA < 3072 is non-compliant |
| PQ algorithm | Must be a NIST post-quantum finalist algorithm | For hybrid certs, both classical + PQ part must be compliant |
| Usage extensions | Certificate must be valid for TLS/SSL | Key usage and extended key usage match FIPS requirements |
| Hash function | Must use FIPS-approved hash (SHA-256, SHA-384, SHA-512) | Needed for signatures |
| Staged deployment | Hybrid certificates can be used during transition (classical + PQ) | Only hybrid certs with FIPS-approved classical algorithms are “FIPS compliant” |
✅ Output logic:
- FIPS 203/204/205 compliance →
✅ Yesonly if:- Key algorithm is FIPS-approved and
- PQ/hybrid part exists (post-quantum algorithm)
- Classical TLS, even if key is strong, →
❌ No - Hybrid PQ with approved classical key →
✅ Yes
Example (simplified) Table for Cert Checker Logic:
| Cert Type | Key Algorithm | PQ Algorithm | FIPS Status | PQ Status |
|---|---|---|---|---|
| Classical TLS | RSA-2048 | None | ❌ | ❌ |
| Classical TLS | ECDSA-P256 | None | ❌ | ❌ |
| Hybrid TLS | RSA-3072 | Falcon | ✅ | ✅ |
| Hybrid TLS | ECDSA-P384 | Dilithium | ✅ | ✅ |
What’s next? We can use these tools to help you map your entire organization’s FIPS-compliant posture, and start your journey to be quantum safe by 2030. Download our tool from Docker and feel free to use it and share it! https://hub.docker.com/r/deansmachines/fips_cert_checker_app
Leave a comment